When it comes to protecting your business from cyber threats, two security testing methods stand out: vulnerability assessments and penetration testing. While both help identify security weaknesses, they serve very different purposes and provide distinct value to your organization.
In this guide, you'll learn the practical differences between these approaches, when to use each method, and how combining both creates a robust cybersecurity strategy that protects your business and satisfies compliance requirements.
What Is a Vulnerability Assessment?
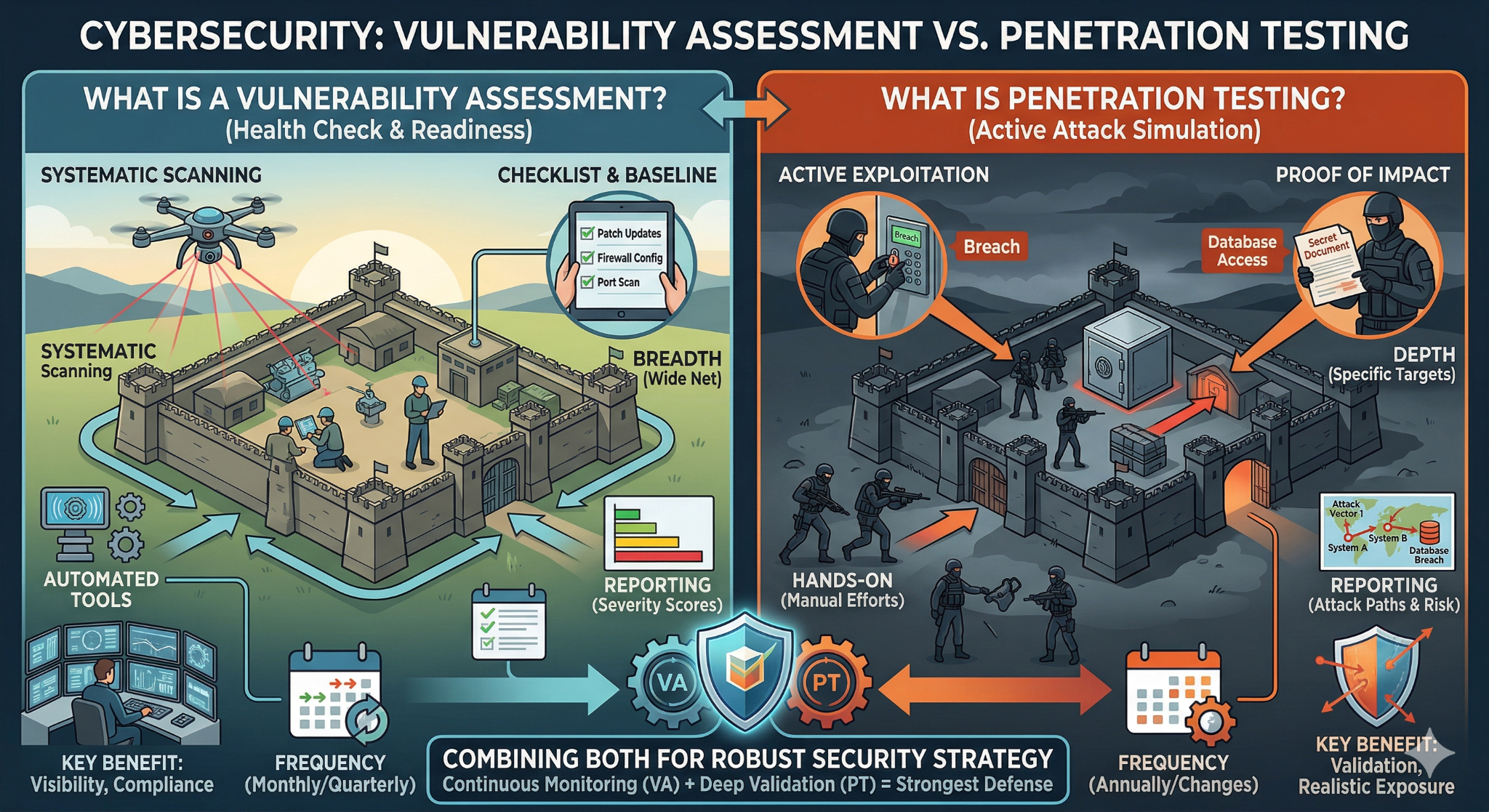
A vulnerability assessment acts like a comprehensive health checkup for your IT systems. It systematically scans your networks, applications, and infrastructure to identify known security weaknesses without attempting to exploit them.
Think of it as getting a detailed inventory of every unlocked door and window in your digital environment. The assessment uses automated scanning tools to examine your systems against databases of Common Vulnerabilities and Exposures (CVEs), which currently contains over 200,000 documented security flaws.
These scans typically complete within 1-3 days and generate comprehensive reports listing discovered vulnerabilities. Each finding receives a severity rating using the Common Vulnerability Scoring System (CVSS), helping you prioritize remediation efforts.
"Vulnerability assessments give us the visibility we need to stay ahead of emerging threats. It's like having a security radar that constantly monitors our digital perimeter," says Richard Fullbrook, Chief Operating Officer at Sirkit.
What Vulnerability Assessments Identify
- Outdated software and missing security patches
- Misconfigured security settings and permissions
- Weak authentication mechanisms
- Unnecessary open ports and running services
- SSL/TLS certificate vulnerabilities
- Database security weaknesses
- Web application security gaps
What Is Penetration Testing?
Penetration testing takes security evaluation to the next level by simulating real cyberattacks. Instead of just identifying potential weaknesses, skilled security professionals actively attempt to exploit vulnerabilities to demonstrate their actual impact on your business.
This hands-on approach mirrors the tactics, techniques, and procedures used by actual cybercriminals. According to IBM's 2024 Cost of a Data Breach Report, the average cost of a data breach reached $4.88 million, making penetration testing a critical investment for validating your security controls.
Penetration tests typically span 2-6 weeks, depending on scope and complexity. Unlike vulnerability scans, these tests provide proof of exploitability by demonstrating exactly how vulnerabilities could be chained together to achieve specific attack objectives like accessing sensitive databases or compromising administrative accounts.
"Some vulnerabilities don't matter on their own, but when chained together can become incredibly powerful. Penetration Testing allows us to see the full picture, and how risks can actually be exploited. This allows us to define what the risk actually is, not just the theoretical potential," notes Richard.
Types of Penetration Testing
- Black box testing: Testers have no prior knowledge of your systems
- White box testing: Full access to system documentation and architecture
- Gray box testing: Limited system knowledge simulating insider access
- External testing: Attacks launched from outside your network perimeter
- Internal testing: Simulated insider threats and lateral movement
- Social engineering assessments: Testing human vulnerabilities through phishing and other tactics
Key Differences: Scope, Depth, and Frequency
The fundamental difference lies in breadth versus depth. Vulnerability assessments cast a wide net across your entire IT environment, examining every accessible system for potential weaknesses.
Penetration tests focus on specific targets, diving deep to exploit discovered vulnerabilities and demonstrate real-world attack scenarios.
Reporting and Actionability
Vulnerability assessment reports provide extensive technical details about discovered weaknesses, complete with remediation steps and priority rankings.
Penetration test reports focus on successful attack paths and business impact. They translate technical vulnerabilities into executive-level risk assessments, showing how security gaps could affect operations, compliance, and revenue.
Timing and Frequency
Most organizations conduct vulnerability assessments monthly or quarterly as part of ongoing security monitoring. The automated nature makes frequent scanning practical and cost-effective.
Penetration testing typically occurs annually or after major infrastructure changes. The intensive manual effort and higher costs make frequent testing impractical, but the deep insights justify the investment.
When to Choose Each Approach
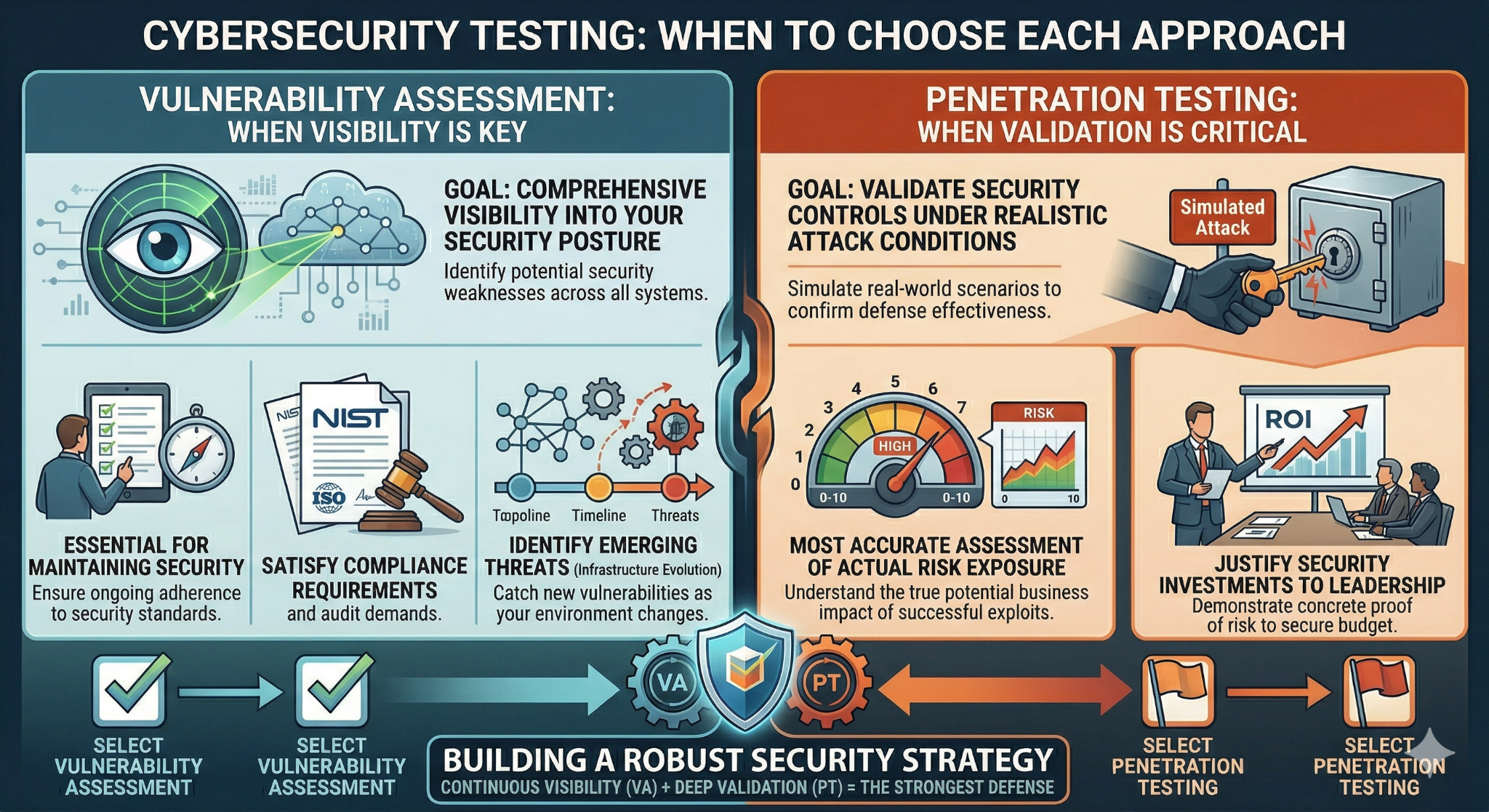
Select vulnerability assessments when you need comprehensive visibility into your security posture. They're essential for maintaining security baselines, satisfying compliance requirements, and identifying emerging threats as your infrastructure evolves.
Choose penetration testing when you need to validate security controls under realistic attack conditions. This approach provides the most accurate assessment of your actual risk exposure and helps justify security investments to leadership.
Building Your Integrated Security Strategy
The most effective cybersecurity programs combine both approaches strategically. Regular vulnerability scans maintain ongoing visibility into your security posture, while annual penetration tests validate the effectiveness of your security controls.
Start each penetration test by reviewing recent vulnerability assessment results. This ensures testers focus on the most critical security gaps and realistic attack scenarios, maximizing the value of your investment.
At Sirkit, our Secure 2026 program integrates both vulnerability assessments and annual penetration testing. This comprehensive approach provides continuous monitoring with professional validation.
Frequently Asked Questions
How often should vulnerability assessments be performed?
Most organizations benefit from monthly vulnerability scans with quarterly comprehensive assessments. High-risk environments may require weekly scans, while lower-risk organizations might scan quarterly. The frequency should align with your change management processes and risk tolerance.
Can vulnerability assessments replace penetration testing?
No, vulnerability assessments cannot fully replace penetration testing. While scans identify potential weaknesses, only penetration tests demonstrate actual exploitability and business impact under realistic attack conditions. Both serve complementary roles in a comprehensive security program.
Do penetration tests disrupt business operations?
Professional penetration tests are designed to minimize business disruption. Experienced testers work during agreed-upon timeframes, coordinate with your IT team, and avoid activities that could cause system outages or data loss.
What should I do with vulnerability assessment results?
Prioritize remediation based on CVSS severity scores and business impact. Address critical vulnerabilities immediately, schedule high-priority fixes within 30 days, and plan medium-priority items for quarterly maintenance windows. Track remediation progress to measure program effectiveness.
Which approach better satisfies cyber insurance requirements?
Most cyber insurance policies require both approaches. Regular vulnerability assessments demonstrate ongoing security monitoring and due diligence, while annual penetration tests validate your security controls under realistic conditions. Check your specific policy requirements with your insurer.
Ready to strengthen your cybersecurity posture with professional security testing? Contact our team for a consultation to discuss which approach best fits your organization's needs, budget, and compliance requirements.
Tags:
Knowledge Base (KB)