For many organizations, multi-factor authentication (MFA) has become the baseline defense against cyber threats. If employees must verify their identity with a second factor such as a phone approval or one-time code, the assumption is that attackers cannot get in.
Unfortunately, attackers have adapted.
A growing category of attacks no longer tries to defeat MFA directly. Instead, cybercriminals steal the session tokens created after a user successfully authenticates. Once stolen, those tokens allow attackers to access accounts as if they were the legitimate user, bypassing MFA entirely.
For leadership teams responsible for protecting company data, understanding this shift is important. MFA remains necessary, but it is no longer sufficient on its own.
Let’s look at how token theft and adversary-in-the-middle attacks work, why they bypass traditional MFA, and what organizations can do to reduce the risk.
The Role of Session Tokens
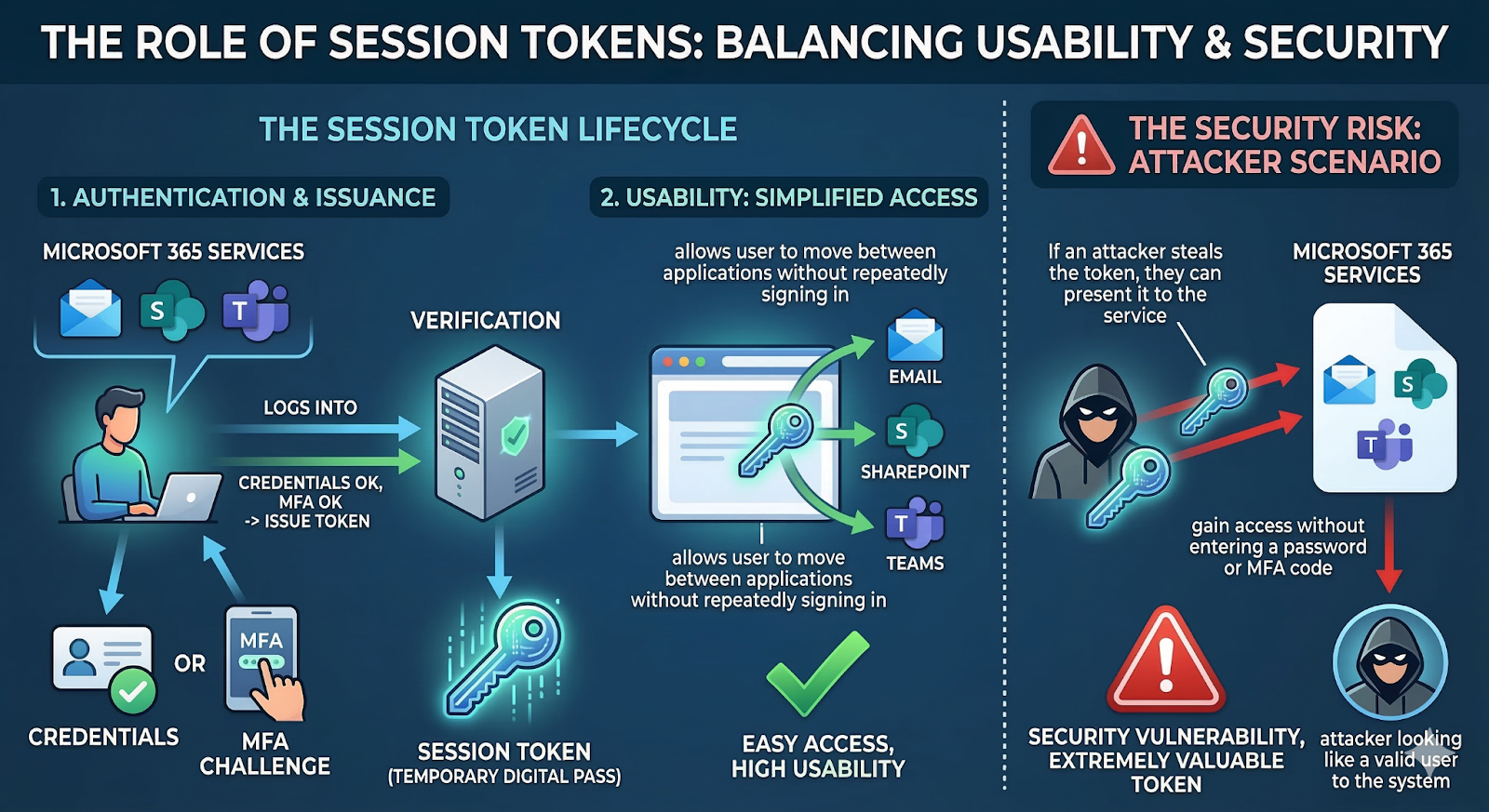
When someone logs into a service such as Microsoft 365, the system verifies their credentials and MFA challenge. After authentication succeeds, the system issues a session token.
A session token acts like a temporary digital pass. It allows the user to move between applications such as email, SharePoint, or Teams without repeatedly signing in.
From a usability standpoint, this makes sense. From a security standpoint, however, that token becomes extremely valuable.
If an attacker steals the token, they can present it to the service and gain access without entering a password or MFA code.
To the system, the attacker looks like a legitimate user.
How Token Theft Happens
Attackers typically obtain tokens through four common methods:
Malware on an employee device
Certain malware can extract authentication tokens directly from browser memory or storage.
Sophisticated phishing sites
Fake login pages designed to mimic legitimate services can capture tokens during the login process.
Compromised or malicious networks
In rare cases, attackers can intercept authentication data on unsafe networks.
Browser vulnerabilities
Occasionally, vulnerabilities allow attackers to access stored tokens.
According to Verizon’s Data Breach Investigations Report, a significant percentage of breaches still involve human interaction, often through phishing. Token theft builds on that reality. Instead of simply stealing a password, attackers now capture the session that follows.
What Is an Adversary-in-the-Middle Attack?
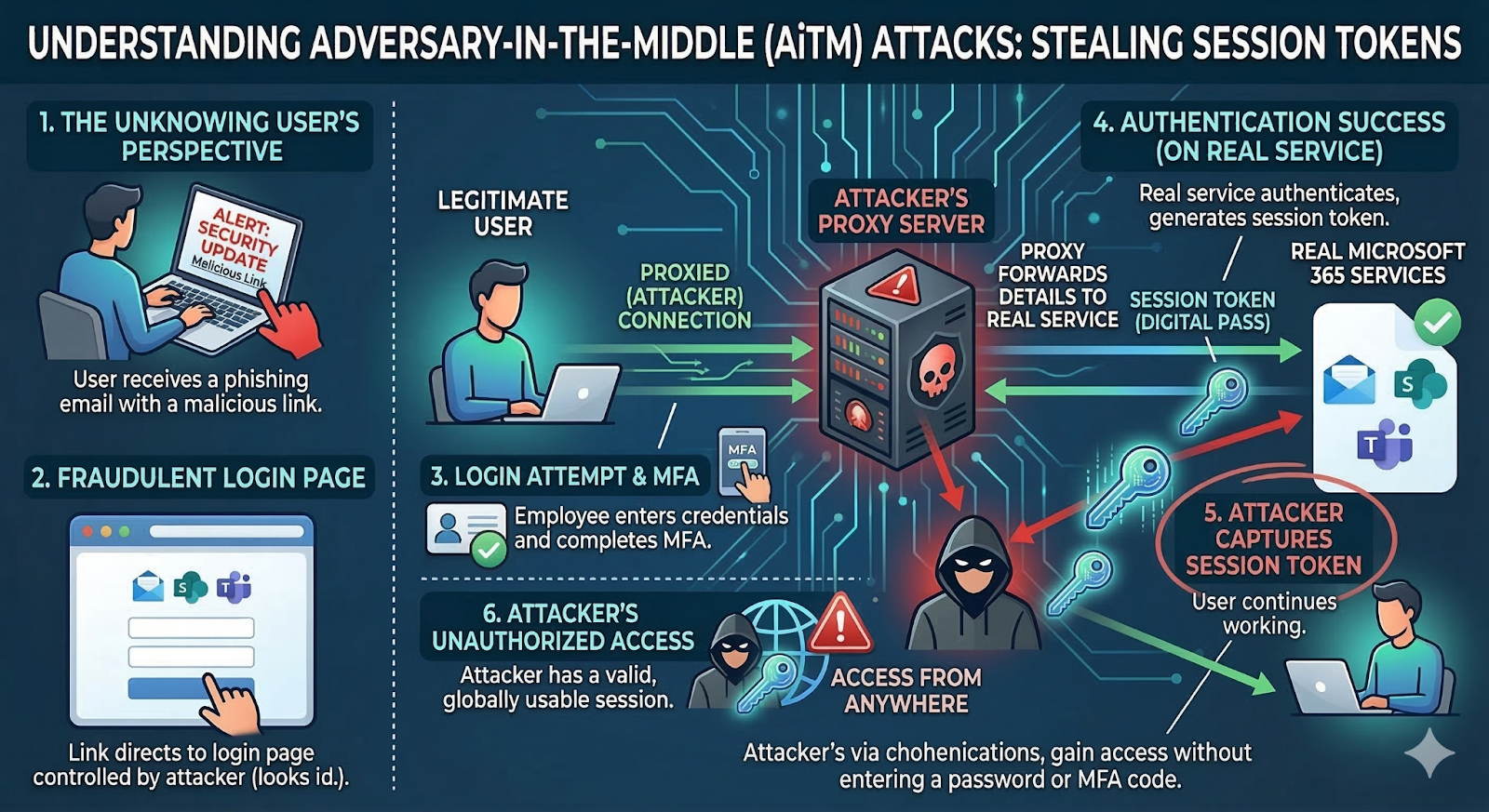
Adversary-in-the-Middle (AiTM) attacks represent one of the most effective ways to steal tokens.
In this scenario, the attacker places a proxy server between the user and the real login service.
The employee believes they are signing into Microsoft 365 or another legitimate system. In reality, they are communicating through the attacker’s server.
Here is how the process typically unfolds:
- The user receives a phishing email with a link.
- The link directs them to a login page controlled by the attacker.
- The page looks identical to the legitimate login screen.
- The employee enters credentials and completes MFA.
- The proxy forwards those details to the real service.
- The authentication succeeds.
- The attacker captures the session token generated during login.
From the user’s perspective, everything appears normal. They log in successfully and continue working.
Meanwhile, the attacker now has a valid session that can be used anywhere in the world.
As Richard Fullbrook, Chief Operating Officer at Sirkit, explains: “The attacker effectively becomes invisible in the login process. From the system's perspective, that token is you, and everything looks legitimate.”
A Practical Example
Consider a finance manager who receives an email requesting them to review a shared Microsoft 365 document.
The link opens a login page that looks identical to Microsoft’s sign-in screen.
The manager enters their password and approves the MFA prompt on their phone.
The login works. The document opens. Unbeknownst to them, the attacker has already captured the session token generated during that login.
Later that day, the attacker uses the token to access the same Microsoft account from another country. They download financial files and internal documents.
Because the session token is valid, the activity appears to be normal user behavior.
Why (and when) Traditional MFA Falls Short
MFA remains a critical security control. However, it should no longer be viewed as the final line of defense. Many organizations now rely on managed IT security programs that combine identity protection, device verification, and ongoing monitoring to reduce the risk of account compromise.
Once authentication completes, most systems assume the session is trustworthy. That assumption is what attackers exploit.
In other words, MFA protects the door, but token theft targets the keys created after you open it. This is why organizations relying solely on MFA may still experience account compromise.
What Organizations Can Do
Reducing token theft risk requires additional layers of protection that verify identity throughout the session, not just at login.
Conditional Access Policies
Modern identity platforms such as Microsoft Entra allow organizations to evaluate ongoing risk signals, including:
- Login location changes
- Device compliance status
- Time-of-day access patterns
- Application-specific restrictions
If activity deviates from normal patterns, access can be blocked or re-verified.
Phishing-Resistant Authentication
Hardware security keys using FIDO2 standards significantly reduce phishing risk because they authenticate directly with the legitimate domain.
Even if a user lands on a fake site, the authentication process fails.
Strong Device Trust
Requiring approved corporate devices adds another verification layer. Even if a token is stolen, the attacker cannot access resources without the registered device.
Shorter Session Lifetimes
Limiting how long tokens remain valid reduces the window attackers can exploit. Sessions that automatically expire after a few hours create fewer opportunities for misuse.
The Leadership Takeaway
MFA remains an essential security control, but it should not be treated as the final line of defense. Attackers have shifted their focus from stealing passwords to hijacking authenticated sessions.
Organizations that treat identity security as an ongoing verification process, rather than a one-time login event, are better positioned to protect sensitive systems. This approach aligns with a Zero Trust mindset, where access is continuously evaluated based on risk.
Token theft and adversary-in-the-middle attacks highlight how cyber threats continue to evolve. Businesses that recognize this shift can strengthen protection without disrupting productivity.
For leadership teams, the takeaway is simple: security is no longer just about verifying who logs in. It is about verifying who remains inside the system throughout the session.
Tags:
Knowledge Base (KB)