Artificial intelligence has fundamentally changed how cybercriminals operate. AI cyber attacks use machine learning to bypass traditional security measures, targeting businesses through automated phishing campaigns, deepfake fraud, and intelligent malware that adapts in real-time.
Unlike conventional threats that follow predictable patterns, these attacks learn from your defenses and modify their approach accordingly.
This shift represents more than just a new tool for criminals, it's a complete evolution in cyber risk that requires businesses and their leaders to rethink their security approach.
The 5 Main Types of AI Cyber Attacks Targeting Businesses
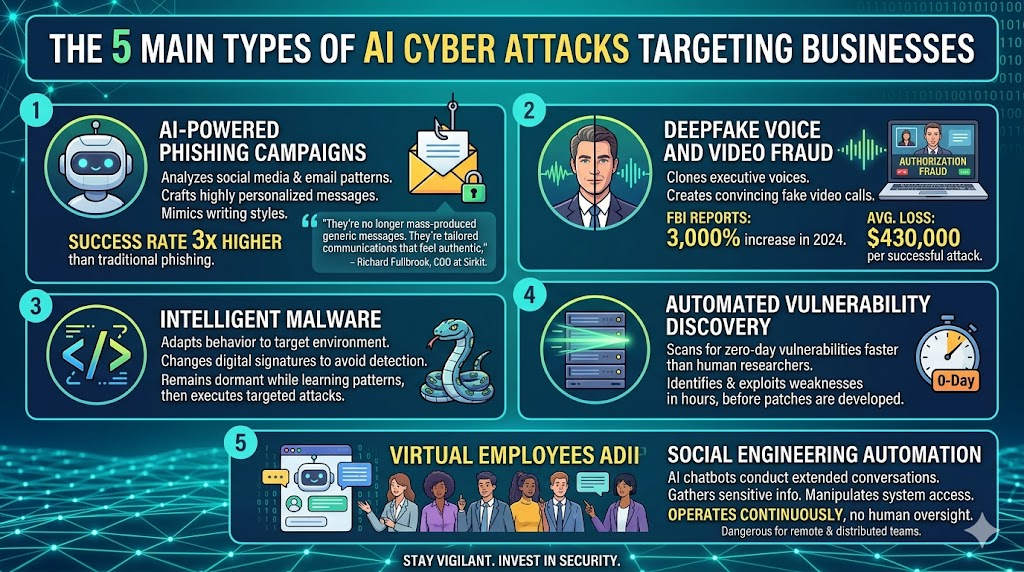
AI-Powered Phishing Campaigns
Modern AI systems analyze social media profiles, email patterns, and publicly available information to craft highly personalized phishing emails. These attacks achieve success rates that are three times higher than traditional phishing because they accurately mimic writing styles and reference specific details about their targets.
"The sophistication of AI-generated phishing emails has reached a point where even security-aware employees can be fooled," says Richard Fullbrook, COO at Sirkit.
"They're no longer mass-produced generic messages. They're tailored communications that feel authentic."
Deepfake Voice and Video Fraud
Criminals now use AI to clone executive voices or create convincing fake video calls for authorization fraud.
The FBI reports that deepfake fraud attempts increased by 3,000% in 2024, with financial losses averaging $430,000 per successful attack.
Intelligent Malware
AI-driven malware represents a significant leap beyond traditional threats. This software adapts its behavior based on the target environment, changing its digital signatures to avoid detection. It can remain dormant while learning network patterns, then execute targeted attacks when conditions are optimal.
Automated Vulnerability Discovery
AI systems can scan for zero-day vulnerabilities faster than human researchers, identifying and exploiting security weaknesses within hours of discovery. This speed advantage gives attackers a critical window before patches can be developed and deployed.
Social Engineering Automation
AI-powered chatbots can conduct extended conversations with employees to gather sensitive information or manipulate them into granting system access. These systems operate continuously without human oversight, making them particularly dangerous for businesses with remote or distributed workforces.
How to Recognize AI Attack Warning Signs
Watch for unusual email patterns from known contacts, including subtle changes in communication style, timing, or terminology that differs from their normal approach.
Be suspicious of unexpected authorization requests via phone or video call, especially for financial transactions or system access. Always verify these requests through a separate communication channel.
Monitor for network traffic anomalies that don't match typical user behavior patterns. These may indicate intelligent malware conducting reconnaissance activities.
Take employee reports of "convincing but strange" communications seriously. Staff members often notice subtle inconsistencies that automated systems miss.
Why AI Attacks Succeed Where Traditional Threats Fail
Traditional cyber attacks follow predictable patterns that signature-based security tools can identify and block. AI attacks continuously evolve their tactics, making detection significantly more challenging for conventional security measures.
While traditional threats typically use mass distribution methods, AI attacks target specific individuals with personalized approaches. This focused strategy achieves higher success rates with smaller-scale campaigns that fly under the radar of broad security monitoring.
The response time difference is critical. Traditional attacks may take weeks to plan and execute, while AI attacks can adapt and pivot within minutes of encountering resistance or detection.
Essential Protection Strategies for Your Business
Implement Comprehensive Multi-Factor Authentication
Deploy MFA across all business systems, with particular focus on administrative access points. Since AI attacks frequently rely on credential theft, additional authentication layers provide essential protection.
Upgrade Employee Training Programs
Train your team to recognize AI-generated content and establish clear verification protocols for unusual requests. CISA recommends monthly cybersecurity training that includes AI threat recognition components.
"Employee awareness is your first line of defense against AI attacks," notes Richard. "But the training has to be specific to AI threats…generic awareness programs aren't sufficient anymore."
Deploy Advanced Email Security
Implement AI-powered email security solutions that can detect AI-generated phishing attempts. Traditional spam filters lack the sophistication needed to identify these advanced threats.
Establish Continuous Network Monitoring
Deploy behavioral analysis tools that can identify unusual network patterns and potential AI reconnaissance activities. Professional monitoring services provide 24/7 oversight that can detect attacks during their early phases.
Conduct Regular Security Assessments
Perform quarterly penetration testing to identify vulnerabilities before AI systems discover them. The Cybersecurity and Infrastructure Security Agency recommends continuous vulnerability assessment in AI threat environments.
Building AI-Resistant Business Processes
Establish verification protocols for all financial transactions and system changes, regardless of the apparent source. This includes callback procedures for voice requests and in-person confirmation requirements for video calls involving sensitive operations.
Implement the principle of least privilege throughout your organization, ensuring employees only access systems necessary for their specific roles. AI attacks often exploit excessive permissions to move laterally through networks.
Develop incident response procedures specifically designed for AI attacks, including clear steps to verify the authenticity of communications during suspected incidents.
The Value of a Professional Cybersecurity Partner
AI-driven threats are moving quickly, and most businesses do not have the time, tools, or in-house expertise to monitor every new attack method on their own. That is where the right managed IT and cybersecurity partner becomes valuable.
At Sirkit, cybersecurity is not treated as an add-on. It is built into the way IT is managed, monitored, and improved over time. Through proactive support, threat monitoring, strategic guidance, and security-first processes, businesses can keep their internal teams focused on day-to-day operations while still having access to specialized expertise when risks become more complex.
This matters because AI-related threats are not always obvious. They can show up through phishing attempts, account takeover, suspicious Microsoft 365 activity, endpoint risks, or gaps in backup and recovery planning.
A managed cybersecurity partner helps bring structure, visibility, and continuous protection to these areas so businesses are better prepared, not just reacting after something goes wrong.

Taking Action Against AI Cyber Threats
AI cyber attacks represent a fundamental shift in cybersecurity risk that requires proactive preparation rather than reactive response. The businesses that invest in AI-aware security measures today will be better positioned to maintain operations and protect sensitive data as these threats continue to evolve.
The key is understanding that traditional security approaches aren't sufficient anymore. Success requires specialized tools, updated processes, and ongoing expertise to stay ahead of attackers who are leveraging the same AI technologies to improve their effectiveness.
Ready to strengthen your defenses against AI-powered threats?
Our team can assess your current security posture and recommend specific measures to protect against these evolving attacks.
Tags:
Knowledge Base (KB)